The average employee receives around 125 emails per day. That's almost 16 an hour. If employees are going to get their actual work done, they can't possibly read every email in detail. For most people, it's a quick check of the sender before moving to the next.
The problem with that approach is the probability that a malicious email will slip through.
Social engineering -- phishing and business email compromises -- is the primary attack method for data breaches. Hackers are playing the odds that sooner or later someone will click on a suspicious email. Helping employees identify questionable emails quickly can reduce the chances of a successful attack. Since 100% of compromised emails come from external sources, flagging emails from external senders is one way to reduce the chances of a successful attack.
External Mail Tagging
Have you seen an email whose subject line looks anything like the following examples?
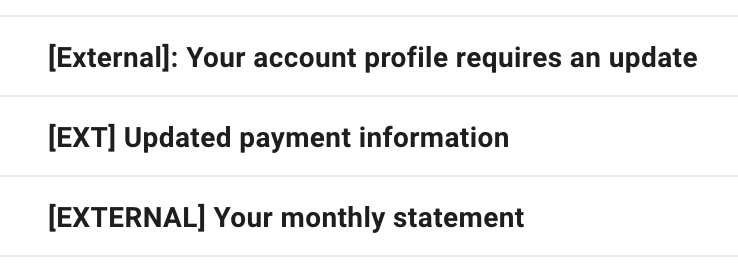
These are each common examples of how savvy administrators of Google Suite, Office 365, and others set up automatic tagging of email messages that arrive from external sources. If you've got a screenful of emails and 13 of them have a subject line that begins with [EXTERNAL], and seven don't, it's pretty darn easy to tell which ones are from inside the company.
Once administrators have implemented tagging, employees are left with an inbox full of [EXTERNAL] messages that they don't know what to do with. Do they delete all of them? Should they move them to a specific folder? Fortunately, administrators can help employees set up filtering to personalize how external emails are handled.
Internal Filtering
Internal filtering provides employees with a tool that can separate [EXTERNAL] emails into categories that align with their job.
Filtering with Intuition
When companies first make the move to marking emails that arrive from the outside as [EXTERNAL] -- or whatever tag they choose -- it's a great idea to ask for feedback from the team on what exactly they find themselves doing with [EXTERNAL] emails. Salespeople and marketers might have a huge portion of their inbox that arrives as [EXTERNAL] and those messages might be completely legitimate.
Outward-facing positions often receive emails containing sales leads, partnership requests, marketing automation workflow messages, and more. However, there may well be another portion of the company (perhaps software developers) who find that almost all of their [EXTERNAL] messages are junk. Having to delete unwanted emails can become an irritant and reduce productivity.
Providing a tagging tool is only the first step in the process. By asking for feedback, administrators can identify routine ways that employees deal with [EXTERNAL] emails. For example, do the software developers typically find themselves manually deleting the bulk of emails that arrive as [EXTERNAL], whereas the marketers find themselves manually moving [EXTERNAL] partnership requests to a specific email folder.
As employees use the tagging tool, they begin to develop a mental model of how to process [EXTERNAL] emails. That's a big step in implementing email security best practices. Adding customized rules can take best practices one step further.
Filtering with Rules
Using rules to filter emails can automate usage patterns, reducing the time employees spend processing emails and the possibility of human error. Suppose those software developers want to automate [EXTERNAL] email deletions. With [EXTERNAL] tagging in place, they can implement rules-based filtering in their inbox (easy for G Suite users and just as easy for O365 users). With a few clicks in the rules configuration, different users can sort their external messages in a way that makes sense based on the amount and legitimacy of external emails that they tend to receive.
Administrators that combine external and internal filtering of emails can improve a company's security posture. They identify the primary source of suspicious emails, but they do not add to an employee's workload. With rule-based filtering, employees have fewer emails to check, making it easier for them to identify questionable requests.
Help with Filtering
Need a hand configuring O365 or G Suite to mark inbound external messages as [EXTERNAL]? We've got you covered -- just let us know if you are ready to implement cybersecurity best practices and we'll get you going with a comprehensive small business cybersecurity program (including, of course, external email tagging).
Feeling adventurous and want to implement [EXTERNAL] tagging on your own? G Suite users, here's a quick video that shows the steps to follow:


